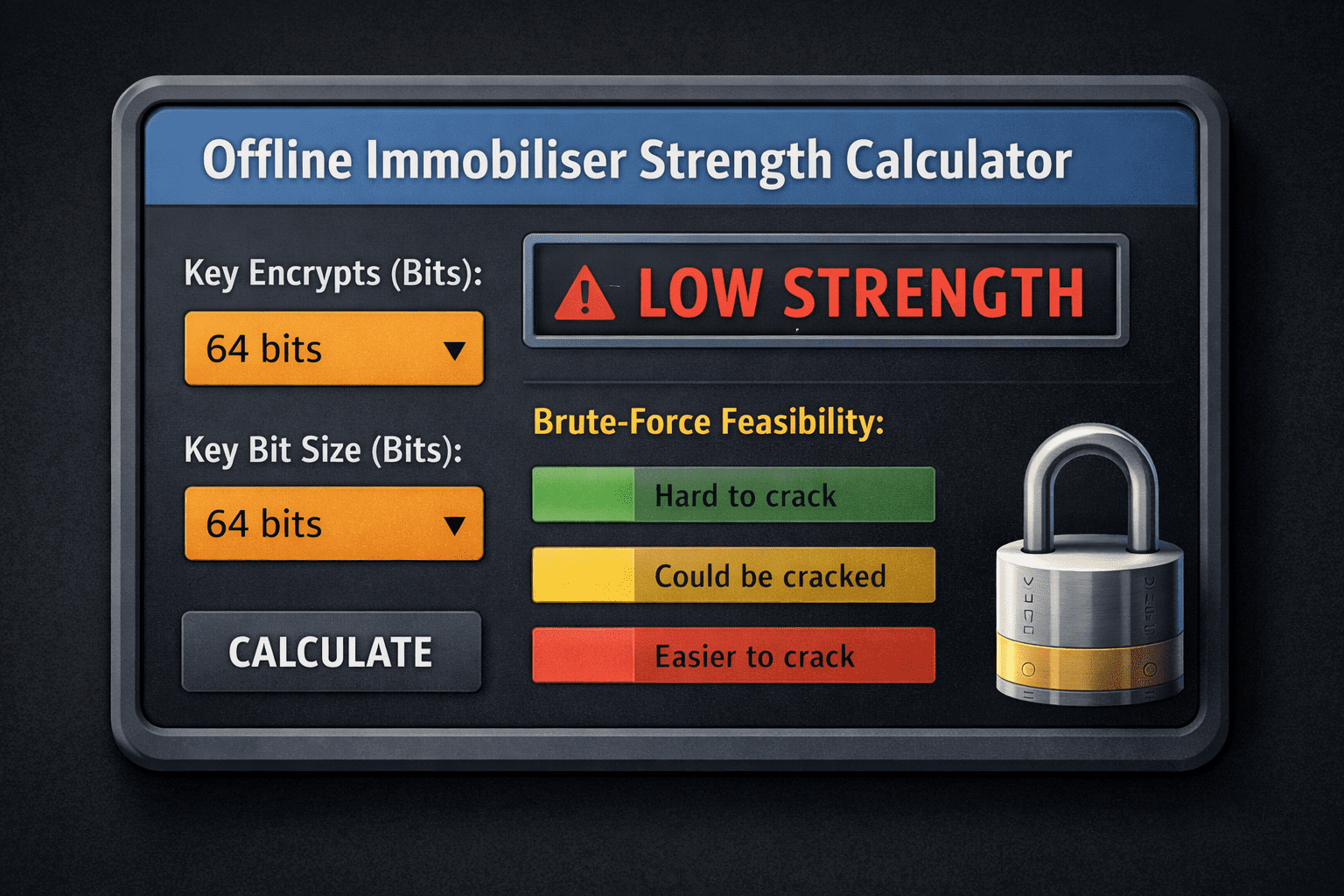
Offline Immobiliser Strength Calculator: Key Size vs. Brute-Force Feasibility
Interactive tool for automotive security hardware that translates common immobiliser key sizes into approximate offline brute-force times. See how private, offline hardware can be more durable against exhaustive search attacks.
Calculator
Results
Notes: These figures are approximate and assume a uniform keyspace and a straightforward brute-force search on a single device. Real-world results depend on parallelization, side-channel considerations, and implementation details.
Formula and methodology
Keyspace size = 2^n. For an unknown key chosen uniformly at random, the average number of trials to find the key is 2^(n−1). On a single device, brute-force time ≈ 2^(n−1) / R, where R is attacker guesses per second.
Security strength is roughly the number of bits n. Higher n increases the work factor dramatically (exponential in n). In practice, design often targets 128 bits or more for long-term resilience, with AES-128/192/256 as common baselines.
Research notes (summary)
- Symmetric keyspace: 2^n possible keys for an n-bit key.
- Average trials to brute-force a random key: 2^(n−1).
- NIST guidance places 128-bit as a common strong baseline for long-term protection.
- AES supports 128/192/256-bit keys; all are currently secure against practical brute-force attacks.
- 40‑bit and 56‑bit keys are considered obsolete due to feasible brute-force attacks with modern hardware.
Tips for using the calculator
-
- Use conservative attacker assumptions for R; consider parallelization and specialized hardware when estimating real-world risk.
- For new immobiliser designs, aim for 128-bit security or higher (AES-128/192/256 baselines).
- Consider multi-factor immobiliser designs (PIN, token, and timing/lockout) to add layers of defense beyond a single key.
- Edge cases: ensure R is a positive number; handle extremely large times gracefully with readable units.
Offline Immobiliser Strength Explained: Key Size and Brute-Force Resistance
Modern vehicle security relies heavily on cryptographic strength, but not all immobilisers offer the same level of protection. This offline immobiliser strength calculator helps translate immobiliser key size into realistic brute-force feasibility, allowing installers, vehicle owners, and fleet managers to understand how resistant a system is to exhaustive key-guessing attacks.
Rather than focusing on brand names or marketing claims, this tool looks at fundamental security strength: how long it would take an attacker to guess a valid immobiliser key if they had offline access and could repeatedly test guesses.
What “Offline” Means in Immobiliser Security
An offline immobiliser is one that does not rely on external networks, cloud services, or live authentication servers. All validation happens locally within the vehicle or immobiliser hardware.
This matters because:
- Offline systems are immune to remote server breaches
- There is no online rate-limiting to save a weak key
- Security depends almost entirely on key size, entropy, and implementation quality
If an attacker gains physical access to hardware, the only remaining defence may be the size of the keyspace and how difficult it is to brute-force.
Understanding Key Size and Brute-Force Time
Key size, measured in bits, defines how many possible keys exist. Each additional bit doubles the search space.
For example:
- 40-bit keys have around 1 trillion possible values
- 64-bit keys are over 16 billion times harder to brute-force than 40-bit
- 128-bit keys are effectively impossible to brute-force with any known technology
This calculator assumes:
- A uniformly random key
- A straightforward brute-force search
- A single attacker device with a defined guess rate
The displayed time represents an average expected time, not a worst-case scenario.
Why Legacy Immobiliser Systems Are Vulnerable
Many older immobilisers rely on:
- Fixed codes
- Low-entropy challenge-response systems
- One-time passcodes with small keyspaces
While these designs were acceptable decades ago, modern hardware can test millions or billions of guesses per second. As a result, 40-bit and 56-bit systems are now considered obsolete for serious theft resistance.
This is why newer standards increasingly target 128-bit security or higher, often using AES-based designs.
How to Interpret the Calculator Results
The calculator outputs four key values:
- Estimated brute-force time
How long an attacker would need on average to find a valid key. - Security strength (bits)
The effective size of the keyspace. - Strength bucket
A practical classification (low, moderate, high) to simplify comparison. - Notes and assumptions
Important context about parallelisation, side-channels, and implementation limits.
If the result shows days, weeks, or even months, that may sound reassuring — but for immobilisers, anything below modern cryptographic baselines should be treated as weak.
Why Attacker Guess Rate Matters
Brute-force feasibility depends heavily on attacker capability. Modern attackers may use:
- Parallel processing
- GPUs or FPGAs
- Specialised cracking hardware
This is why the calculator allows you to adjust guesses per second. Conservative assumptions help avoid false confidence, especially when evaluating high-risk vehicles or fleet assets.
Best Practices for Modern Immobiliser Design
For long-term resilience, security engineers and installers should aim for:
- 128-bit key strength or higher
- Well-reviewed cryptographic primitives (AES-128/192/256)
- Secure key storage within hardware
- Lockout, timing delays, or multi-factor checks
- Resistance to side-channel attacks
Key size alone does not guarantee security, but insufficient key size guarantees failure.
Who This Calculator Is For
This offline immobiliser strength calculator is useful for:
- Vehicle owners evaluating aftermarket immobilisers
- Installers comparing legacy vs modern systems
- Fleet managers assessing theft risk
- Security-conscious buyers researching immobiliser categories
- Engineers reviewing keyspace adequacy
It is intended as an educational and comparative tool, not a certification or penetration test.
Final Notes on Offline Immobiliser Security
Offline immobilisers can be extremely durable against attack — but only when designed with modern cryptographic strength in mind. As compute power continues to increase, systems that rely on small keyspaces become progressively easier to defeat.
Use this calculator to understand why key size matters, identify weak designs, and make informed decisions before installation.
For installation planning and verification steps, continue to the offline immobiliser install prep checklist to ensure the system is deployed correctly and securely.
Offline Immobiliser Install Prep Checklist